Nathan Gardels is the editor-in-chief of Noema Magazine. He is also the co-founder of and a senior adviser to the Berggruen Institute.
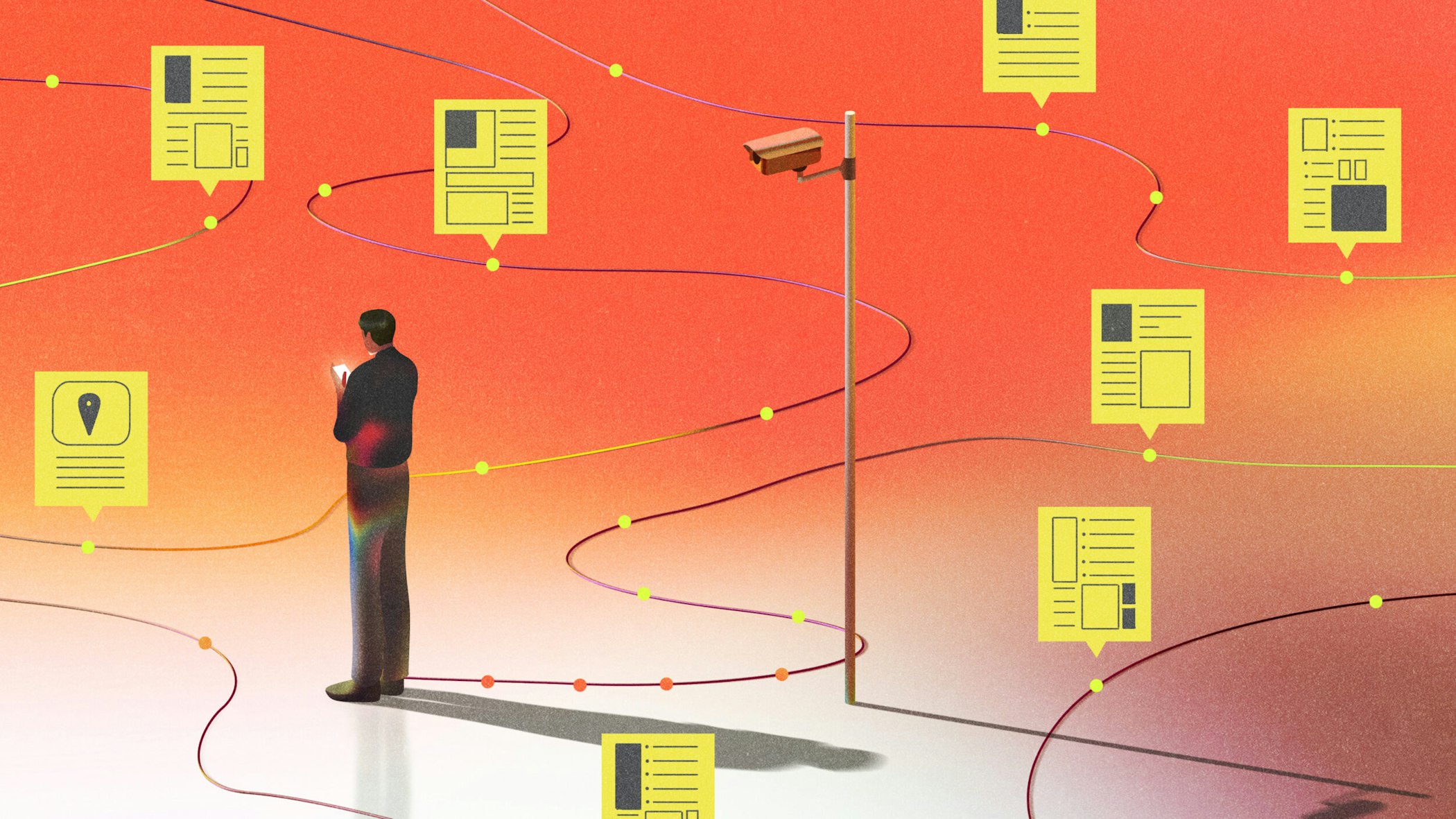
During the Covid pandemic in China, state surveillance, enabled and abetted by new technologies, expanded exponentially in the name of public health.
Citizens were assigned color-codes and access requirements that determined where they could and could not go, enforced by cameras outside people’s homes, divided into neighborhood grids for continuous monitoring of movements. Cross-referencing network connectivity allowed unprecedented data aggregation that put it all together with travel history, online shopping patterns, cell phone use and ID numbers.
Though considered necessary measures at the time to stem contagion, it was predictable that, once the pandemic was over, the state would also use the infrastructure it had built for political monitoring and control. That has, in fact, happened, further enhanced by new facial recognition technology and the ubiquitous expansion of camera coverage. It is estimated that there is one camera for every two citizens in China today.
Like most of us in the West, I was used to surveillance capitalism tracking my personal online activity for marketers to sell me what I didn’t know I needed. I acquiesced for convenience and access. But back during the Covid days of 2019, I still dismissed the possibility that the government in America could ever go in China’s direction.
I think differently in 2026, just as I do about the once-distant possibility of election tampering, government-backed retribution against political enemies, the politicization of the Justice Department, the demonization of the courts and the erosion of the rule of law.
It is deeply distressing not only that two people were shot to death by masked ICE agents in their Minneapolis campaign to root out immigrant criminals, but that the victims were non-criminals and U.S. citizens. What is most alarming in the long term is that the surveillance apparatus put into place to track criminals is already being used on dissenting activists.
As The New York Times reports, on January 10, Nicole Cleland, an activist monitoring ICE activities in Minnesota, was stopped by an agent. Though the two had never met, the agent walked over to her car and surprised her by addressing her by her name. He told her she was registered by his face-recognition technology, which was connected to an ID database.
Various tech companies, such as Clearview AI, Inc. and Palantir Technologies, are working with ICE to provide data analytics that link cellphone use, social media and online activity with other government and commercial data to identify people’s real-time locations, according to the Times investigation.
According to current and former Department of Homeland Security officials contacted by The Times, “technologies are being used not only to identify undocumented immigrants but to also track citizens who have protested ICE’s presence.”
This is where it begins. Just as pandemic-related surveillance morphed into a comprehensive system of monitoring in China, so too the surveillance mission of tracking immigrant criminals is bound to creep, as it already has, into political life even in the U.S.
“Today’s AI-enhanced connectivity applied to political ends is a game changer in the embryonic stages of mission creep. The warning lights should be flashing red.”
Once the infrastructure is in place for one purpose, the risk is greater than not for it to be used for other purposes. Just to start with, bad elements or “dangerous criminals” are a political determination, as when the heads of Homeland Security and ICE pre-emptively labeled the fatally shot Minnesotan Alex Pretti a “domestic terrorist.”
Long suspicious of state authority, I never imagined that America would reach a point where our constitutional protections are teetering because the latest innovations in technology are converging with demagogic politics to corrode the institutional checks and balances by which republics endure.
When I was 17, I registered my opposition to the Vietnam War by not registering for the draft. In those days, that was a felony offense carrying a five-year prison sentence, for which I was prepared to suffer for my convictions.
Then-President Richard Nixon drew up an “enemies list” of opponents to the war, tapping their phones, investigating them through the Internal Revenue Service and otherwise seeking to discredit them. He set loose the FBI, which regularly surveilled anti-war activists across the country and on university campuses. Civil libertarians were appalled.
Though hardly a prominent figure in the anti-war movement, I learned later, when obtaining my FBI files through the Freedom of Information Act, that during the summer of 1972 and winter of 1973, the FBI tracked down my whereabouts and activities on eight different occasions in four different cities through personal surveillance or by surreptitiously obtaining information from “friends of friends” and relatives.
In those days, there was no way to cross-reference all known information about me, culled out by AI from some database. So, for all their snooping, the FBI never discovered that I didn’t register for the draft, for which I could have been arrested on the spot. (When Jimmy Carter was elected president in 1977, he declared an amnesty for all draft resisters.)
In our fevered youth, we regarded the lame bureaucratic inefficiency of those years as the makings of a police state. Had we only known what the real thing might look like.
Today’s AI-enhanced connectivity applied to political ends is a game changer in the embryonic stages of mission creep. The warning lights should be flashing red. No one should be so naïve as to think that all that information about us, compiled into profiles accessible through advanced cross-referencing search software, will stay in those private silos should someone in authority want it.
What all this makes clear is that, where there is connectivity, there is surveillance.
It has been said that every politician is an opportunist; the question is which opportunity they take. So, too, the question going forward is how these powerful tools, once available, will be used, by whom, against whom and to what end.